Role Based Access Control (RBAC)
Oracle Fusion Security is based on Role Based Access Control model.
Role based Access control defines who can do what on which functions or sets of data under what conditions.
In Role Based Access Control, we provide users with roles which are assigned access privileges to protected resources.
There are 4 types of Roles:
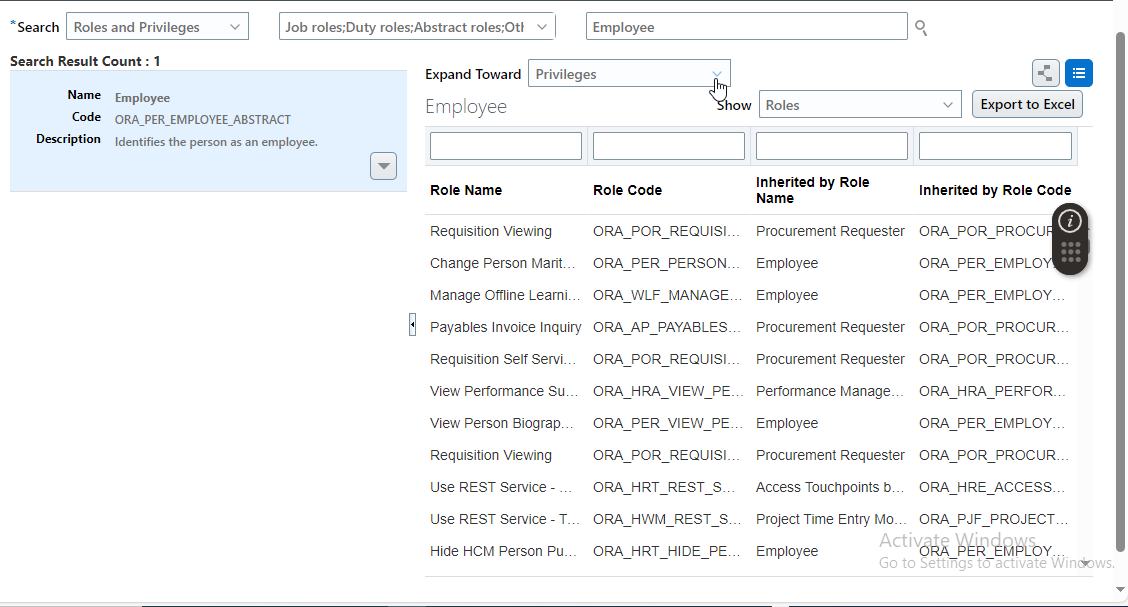
(A) Abstract Role:
Abstract Role gives access to the very basic functionality of Fusion application.
Example, let us say, we hire new employee and want to give access to only basic functionality then we
can assign him abstract role.
Example of Abstract Role: Employee Role
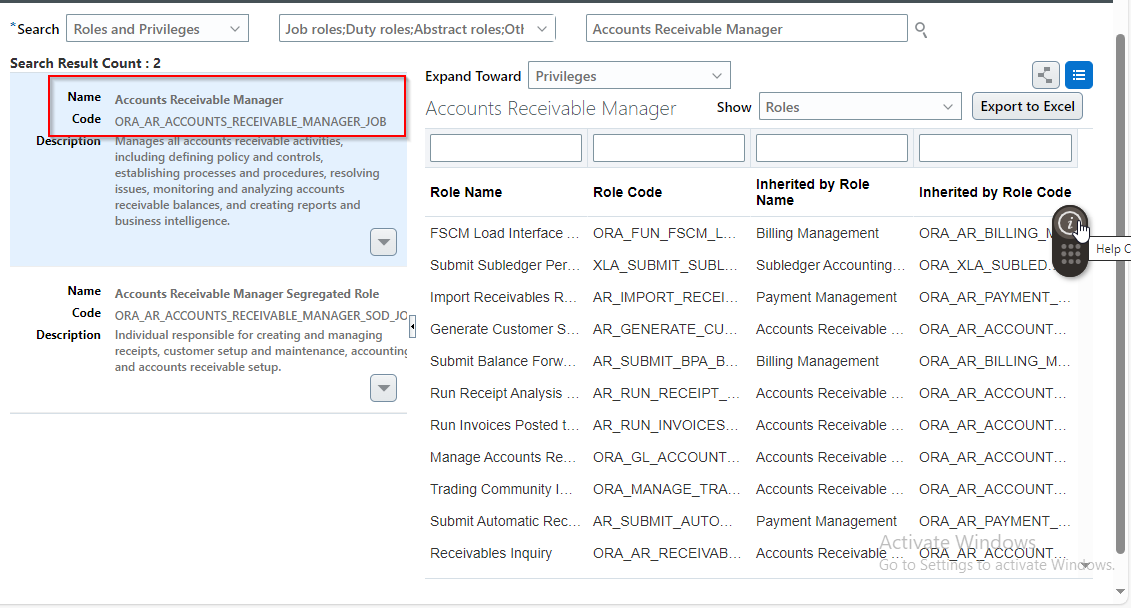
(B) Job Role:
Job Roles give access to users with tasks related to his job.
For Example, if someone is hired to perform AR related task, we need to assign him AR related Job role.
Other example of Job Role: General Accounts, Account receivable Manager, Human Resources specialist.
(C) Privileges:
Privileges are grants access to specific tasks, links, and actions within applications. The access controlled by a particular privilege is fixed and can only be changed by an enhancement to the application.
You can control functions and features to which a user has access by grouping desired privileges into duties and assigning duties to job roles which can be then assigned to users.
Example of Privileges:
Create Transactions, Manage Transactions etc.
(D) Duty Role:
Duty roles represent a logical collection of privileges that grant access to tasks that someone performs as part of a job.
Job and abstract roles permit users to carry out actions by virtue of the duty roles they include.
Each predefined duty role consists of logical grouping of privileges that represents the individual duties that users have as part of their job.
Duty roles are composed of security policies which grant access to work areas, task flows, application pages, reports, batch programs and so on. We can create custom duty role and can include predefined and custom duty role in custom role and abstract roles.
We cannot assign Duty Roles directly to the user.
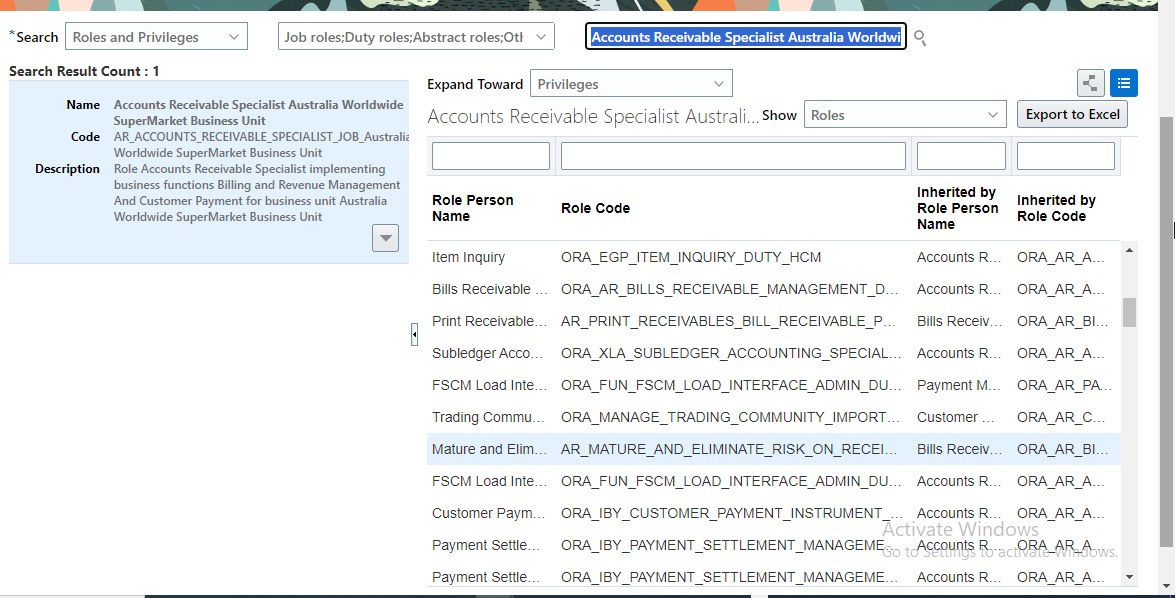
Below is an example of DUTY role.
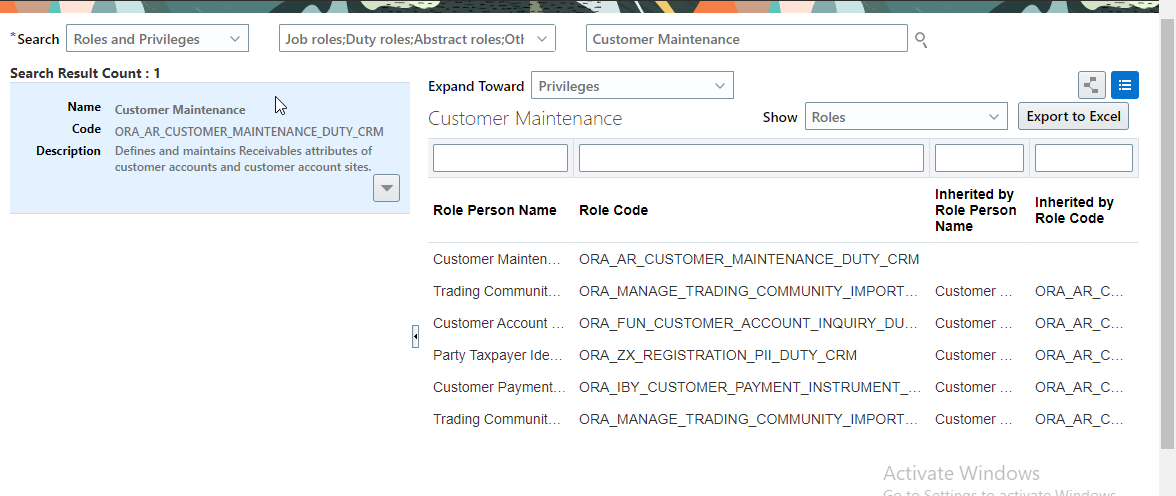
Duty role consists of function security privileges and data security policies. Duty Role may also inherit aggregate privileges and other duty role.
(E) Data Role:
Data Roles are based on job roles, which means it is a blend of user’s job role and data that employee is given access to. Data Role offers the data that the user can act upon. They define the data instance on which the job role can be performed. These roles define the data instance without which the user cannot access any data from the system.
Data Roles inherit job roles and add data scope to it.
Example, Accounts receivable specialist in the Australia Business unit may be assigned the data role Accounts Receivable Specialist Australia Worldwide Supermarket Business Unit. This data role inherits job role Accounts receivable specialists and grants access to transactions in Australia Business unit. Data roles are created and maintained using data role templates in Authorization Policy Manager (APM).
Data Roles are not used after R12 release in Oracle Fusion. Data Roles are replaced by Manage Data access
(F) Manage Data Access for Users:
This is another way of providing data access to the user based on the role assigned to him.
For example, consider a user who manages accounts payable functions such as processing supplier invoices for US business units. In this scenario, the user must be assigned job roles such as predefined accounts payable manager and given access to US operating business unit.
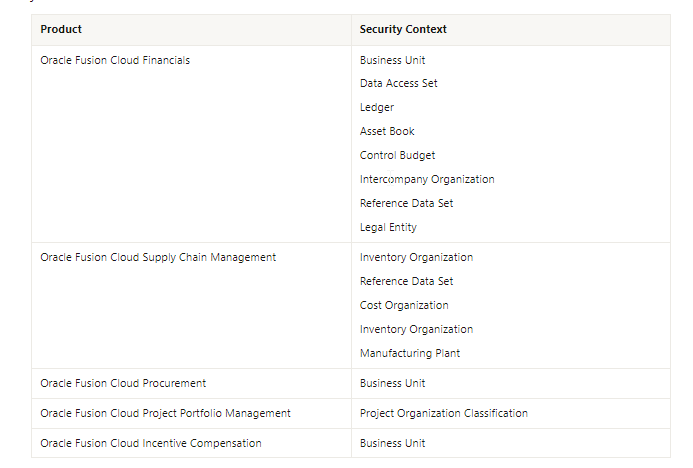
The following table lists the elements of enterprise structure to which users can be assigned access based on their job roles:
Now let us understand practically with examples the meaning of each role and its use.
(F.1) Create new user:
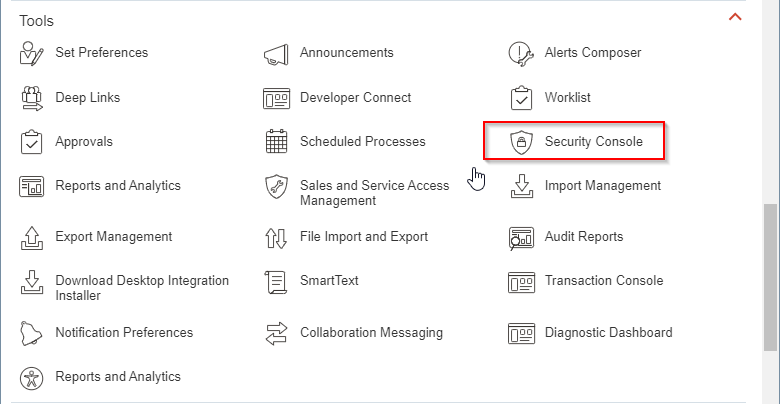
Navigate to Tools —-> Security Console
Go to users:
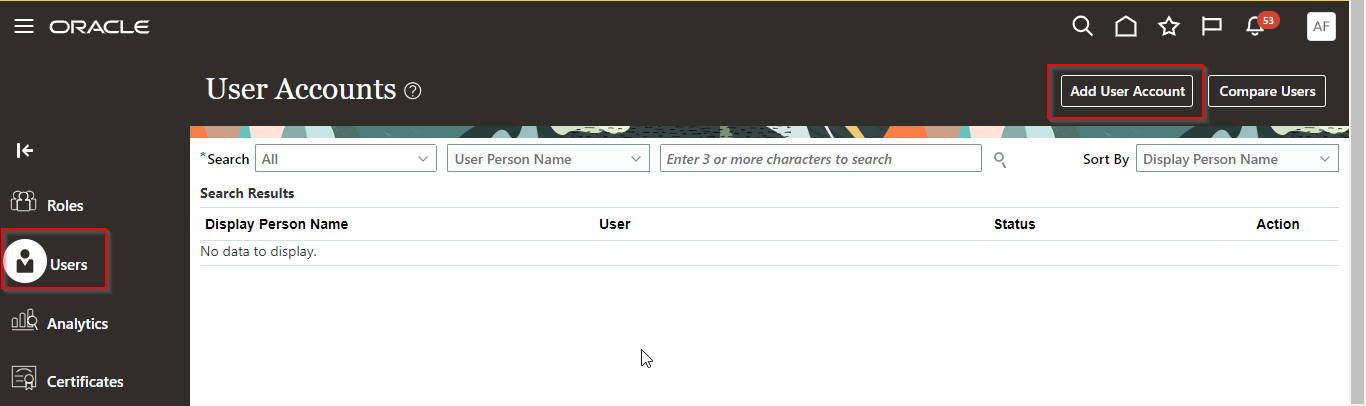
Click on Add User Account
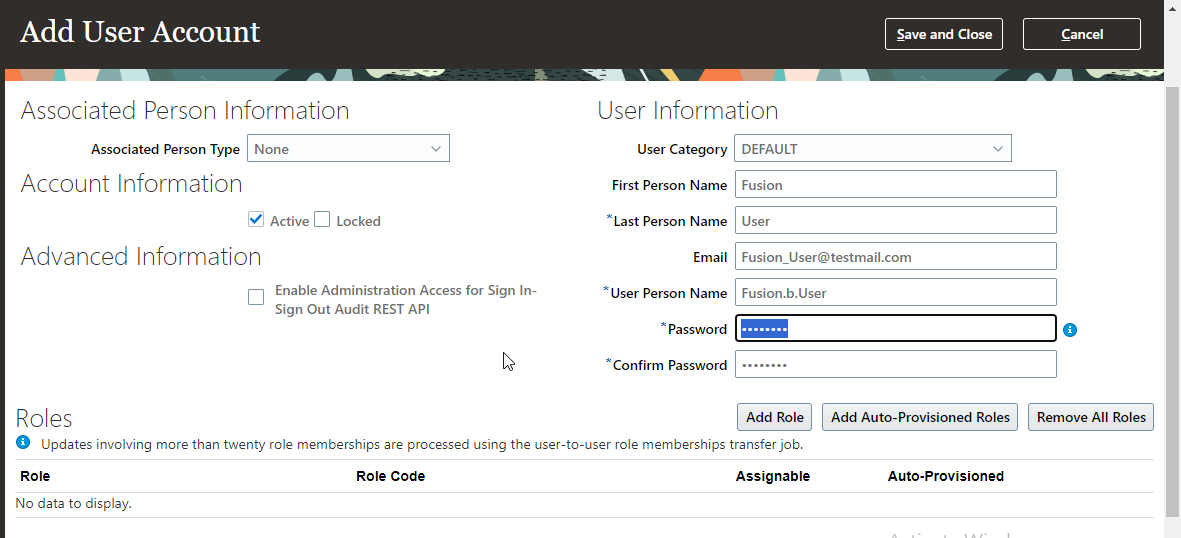
Let us not assigned any role initially and click on Save and close.
Login with new user which is created:
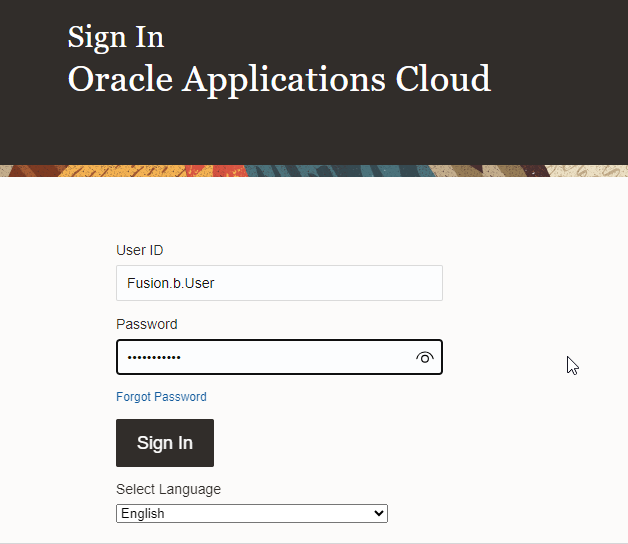
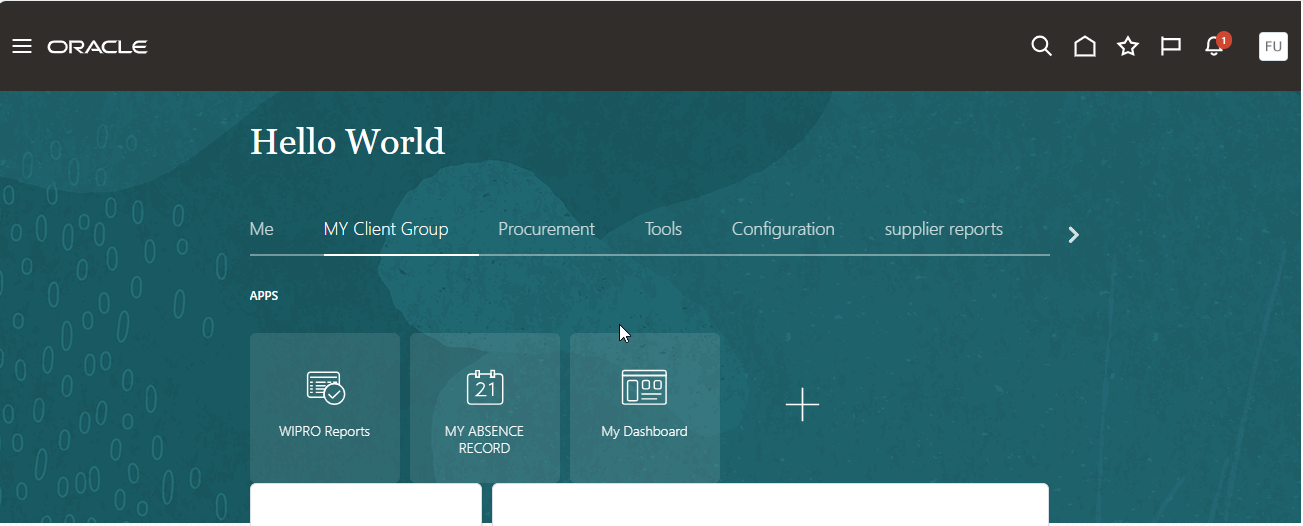
If we see, we don’t have a page to check employee details which is common for any user.
Now let us assign abstract role to this user.
Abstract Role Name: Employee.
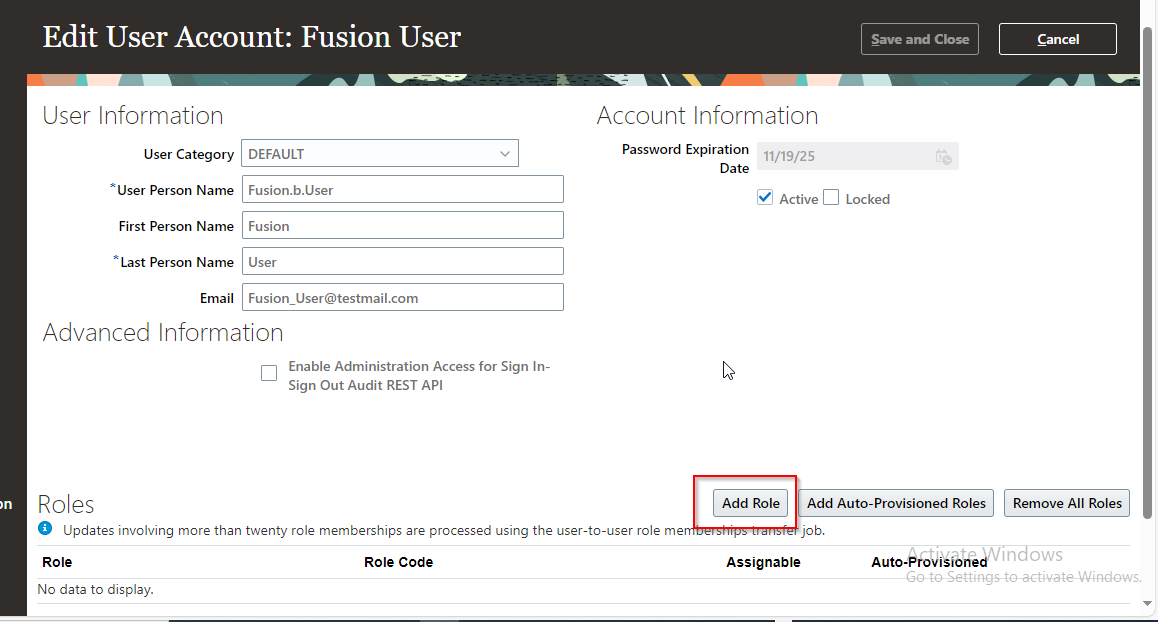
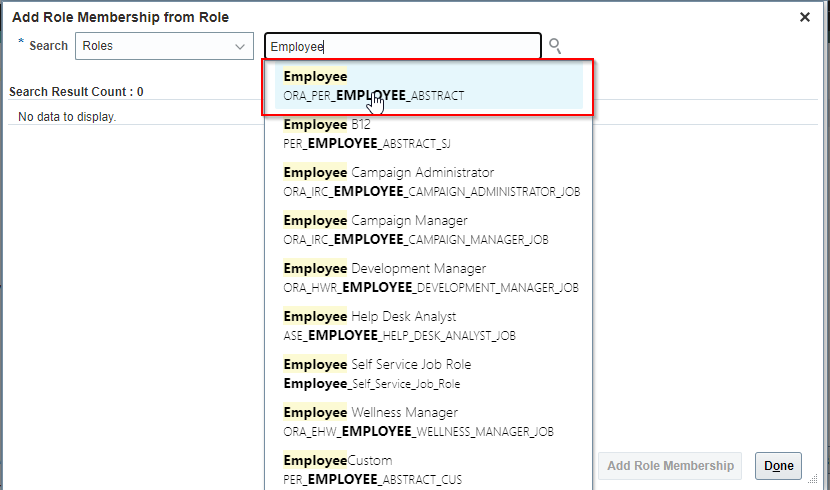
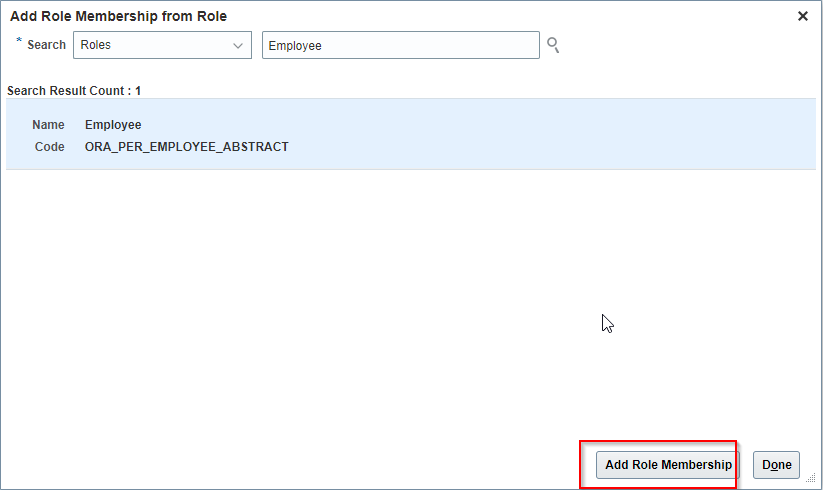
Click on Add Role Membership.
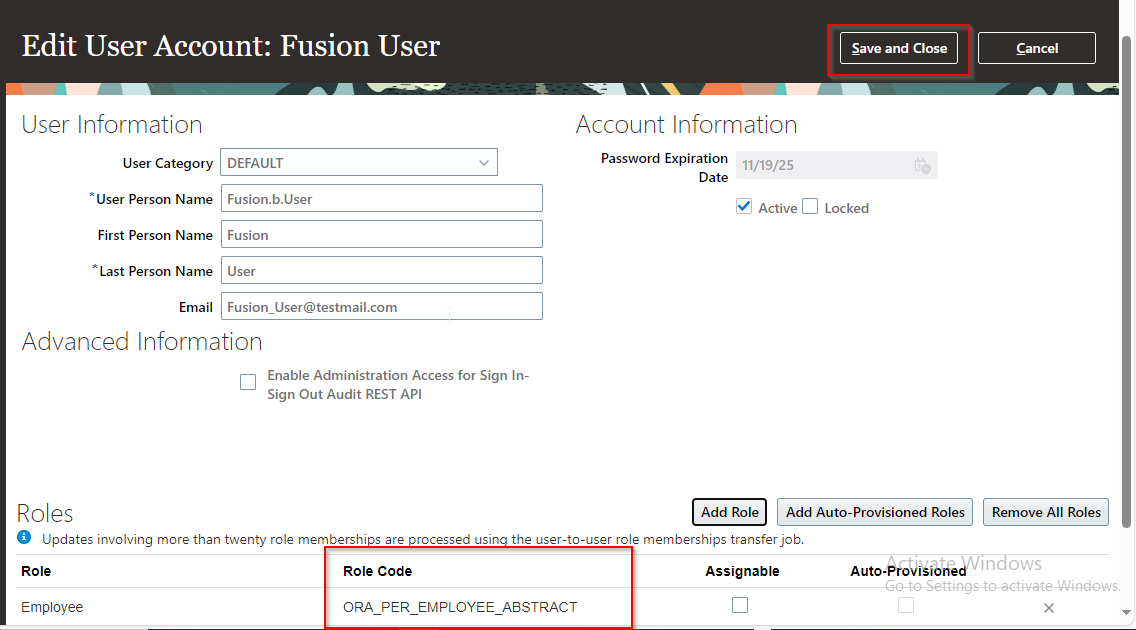
Click on Save and Close.
Now let us login again with the same user.
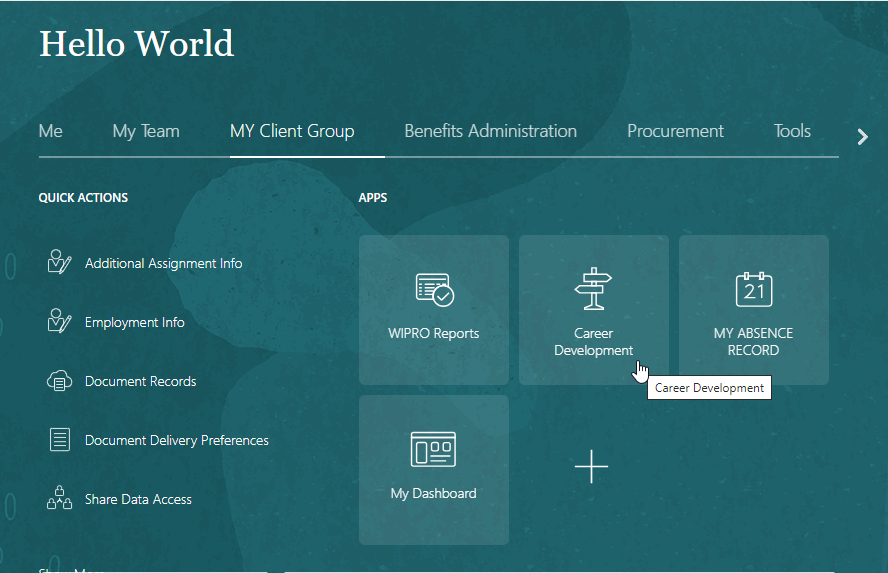
Now we can see, users can access employment info page.
Now let us consider this user is given job to perform task related to Accounts Receivable module. In this case, we need to assign him Job role associated with Accounts Receivable.
Let us add “Accounts Receivable Specialist.” Job role to this user.
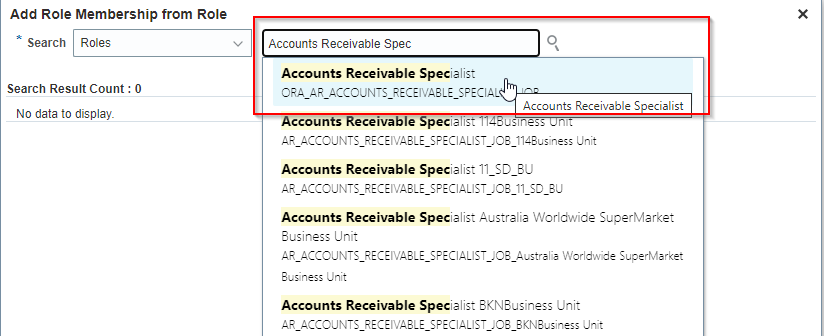
Click on Add Role Membership
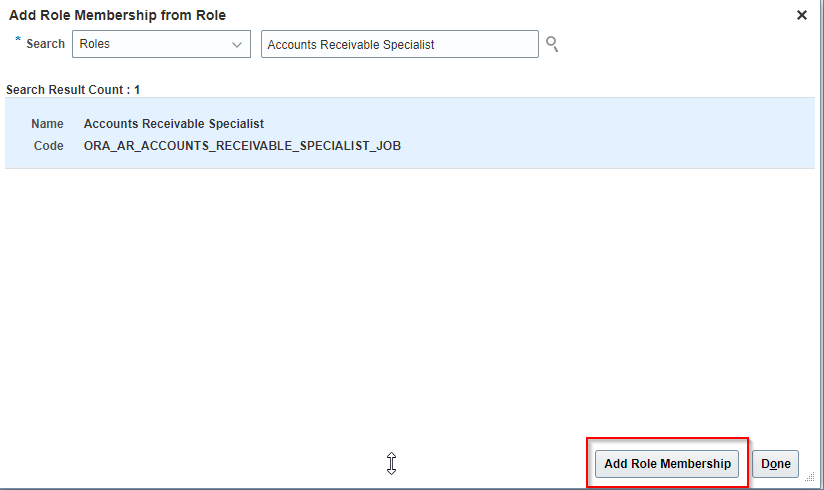
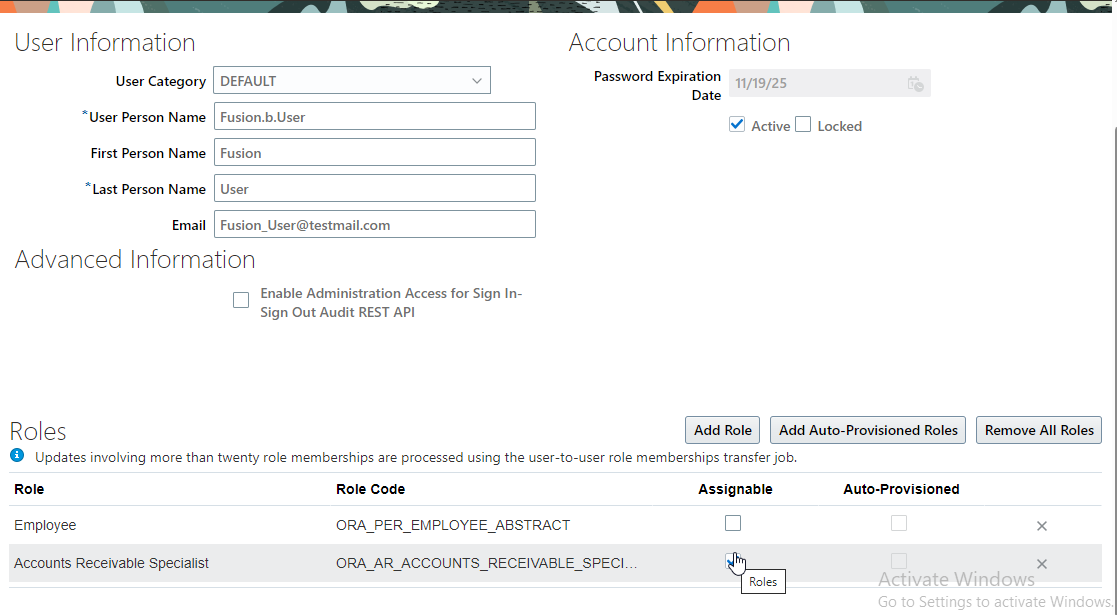
Click on Save and Close.
Now login with the same user.
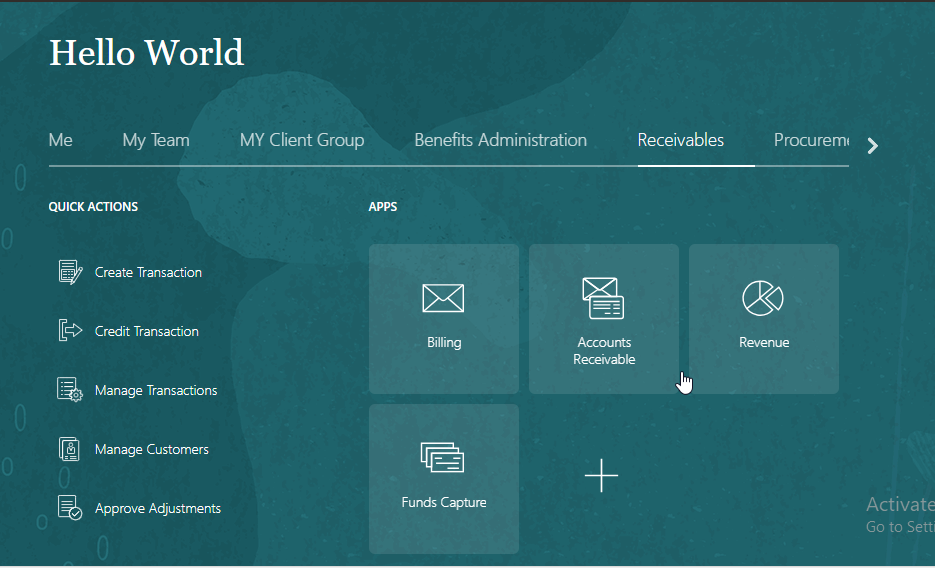
Now we can see Receivable option is enabled for this user.
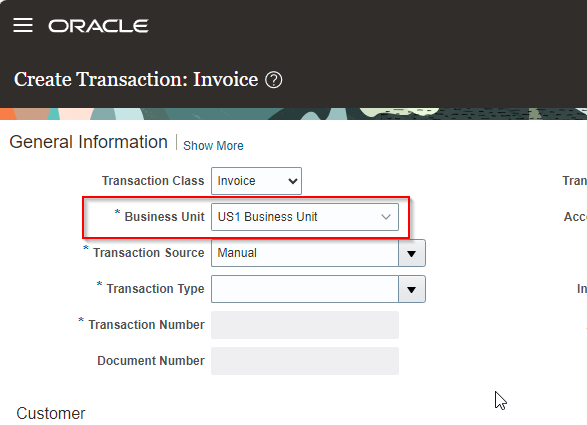
Let us click on Billing and try to create an AR invoice.
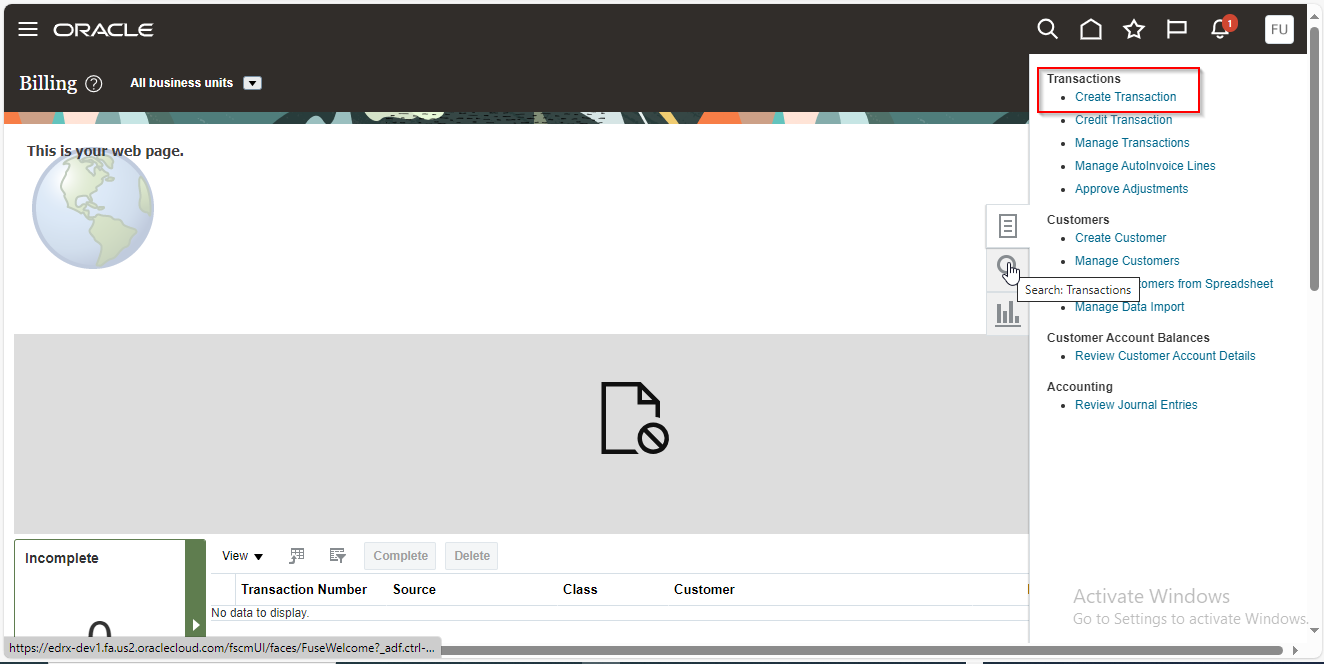
Click on Create Transaction.
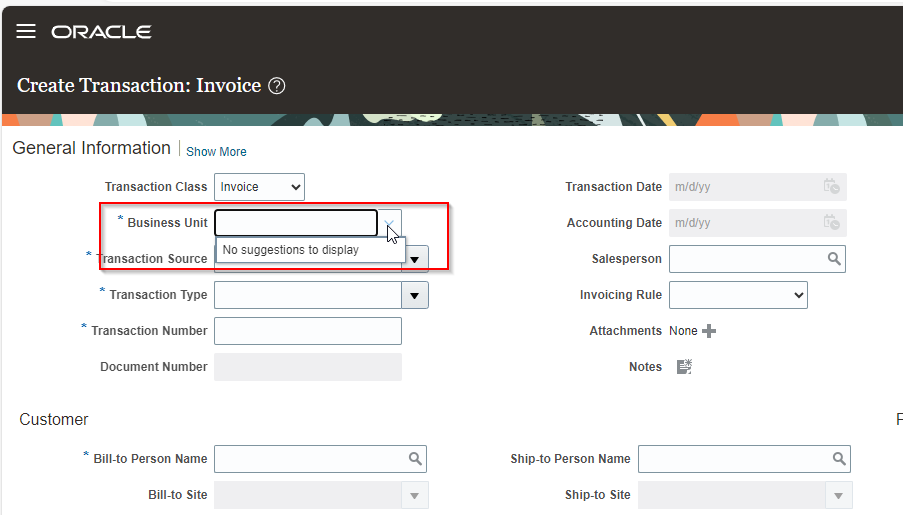
Here we can see create transaction page is enabled for the user but as there are no business units coming in list of values, user cannot create transactions.
To access the business unit, we need to assign data access of that business unit to Accounts Receivable Specialist role.
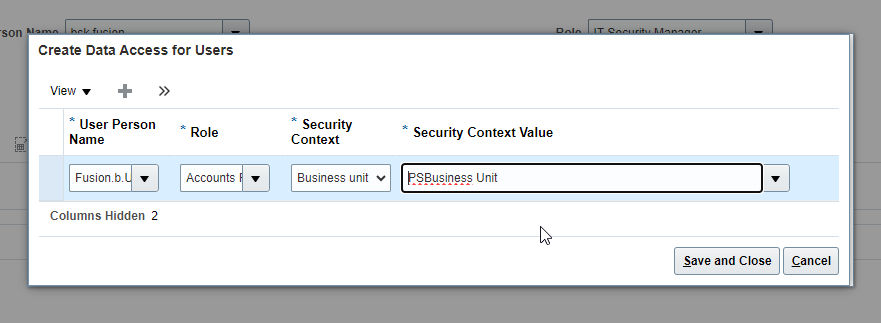
Now let us assign data access for business unit to user.
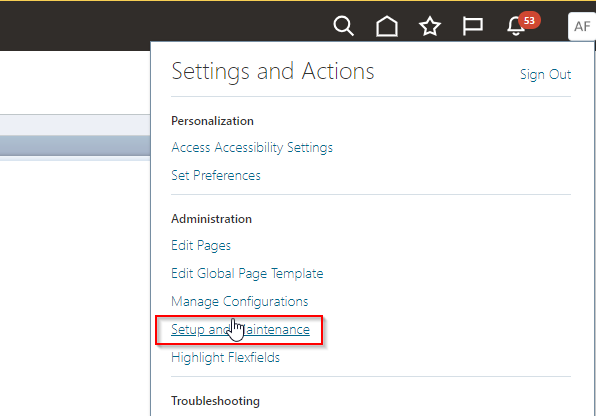
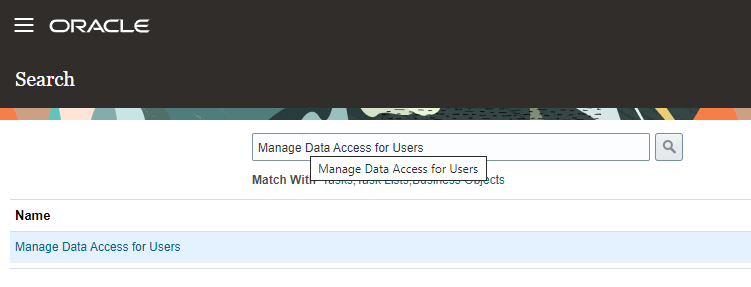
Navigate to Setup and Maintenance
Go to global search.
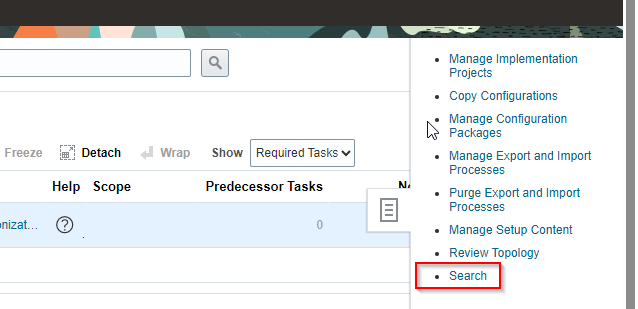
Search for “Manage Data Access for Users”
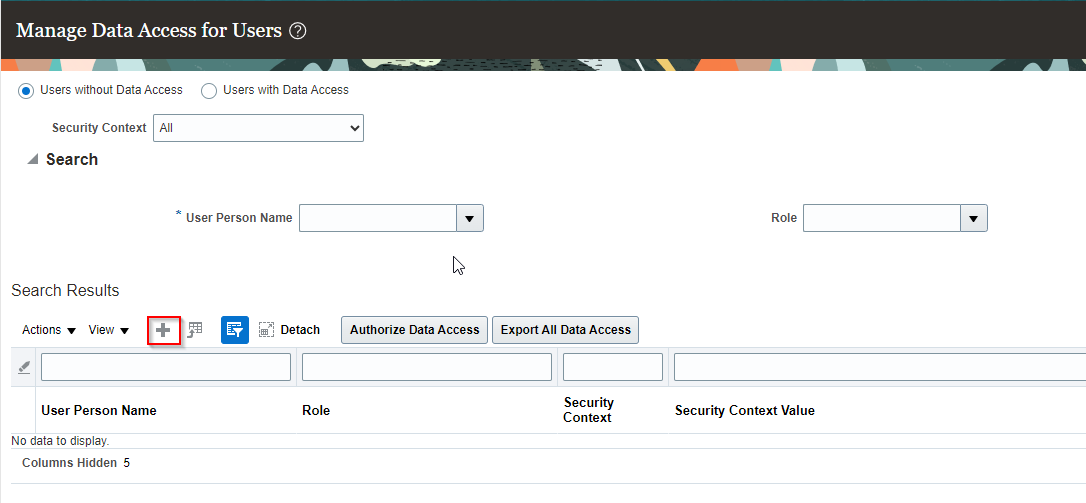
Click on + Icon.
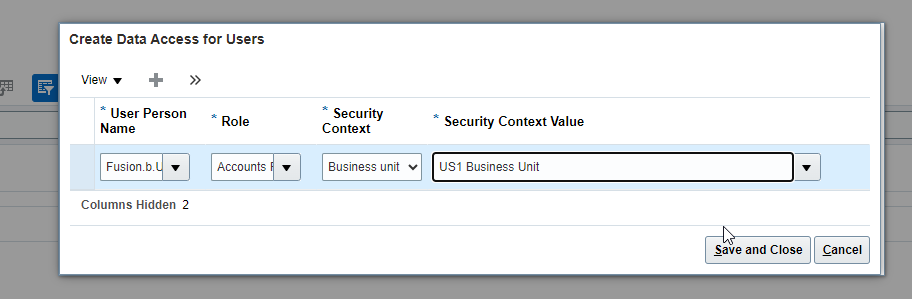
Click on Save and Close and then Done.
Now to cross check, go to Users with Data Access.
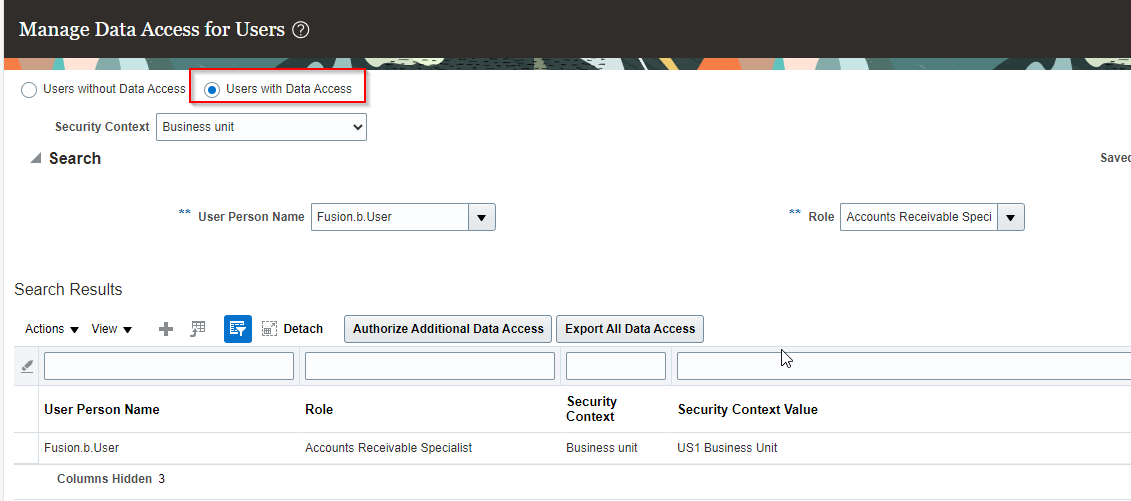
Now data access for US1 Business Unit is assigned to user.
Let us login with the user and go to Create Transaction screen.
Here we can see we got access to create AR Invoice in US1 Business Unit.
Let us add access for another BU to same user.
Click on Save and Close.
Go to “User with Data Access” screen to cross validate assignment.
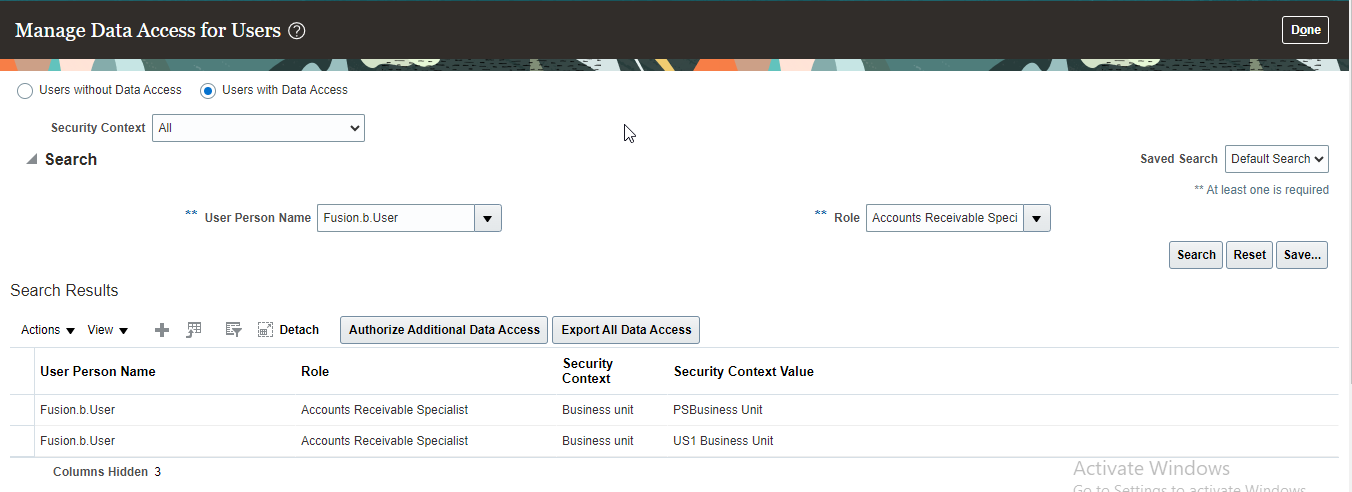
Here we can see, two business units are added now.
Now login with the same user and go to Create Transaction page.
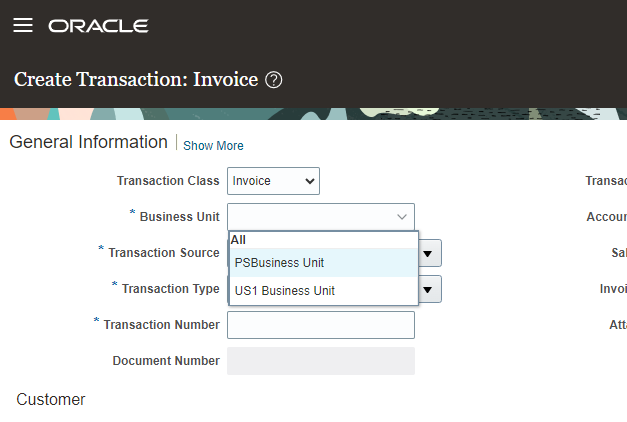
Now here we can see two business units.
(G) Security Policies:
A Security policy is a unique association between a duty role and a privilege.
Each Duty Role can include one or more security policies.
There are two types of Security policies:
(G.1) Functional Security Policies:
This represents “WHO CAN DO WHAT”
Functional Security Policy is a unique association between a duty Role and functional Privilege.
Functional Security policies are defined via function Security Privileges.
Each Function Security privilege secures the code resources that make up relevant pages, page components (like Tab and button) and scheduled Job.
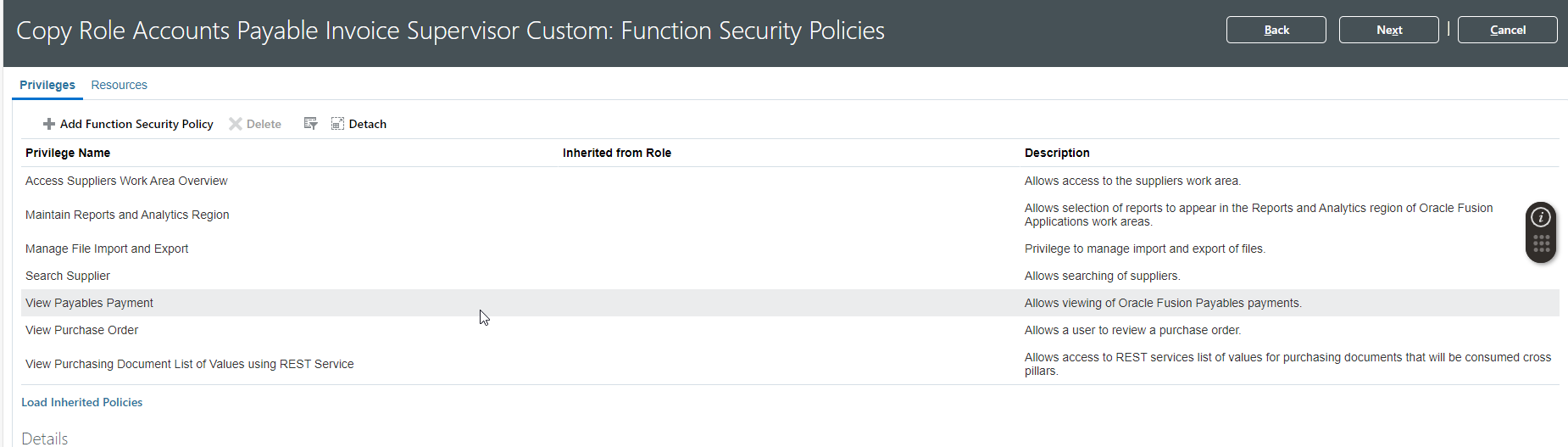
Let us consider below Function Security Policies for Accounts Payable Invoice Supervisor Role:
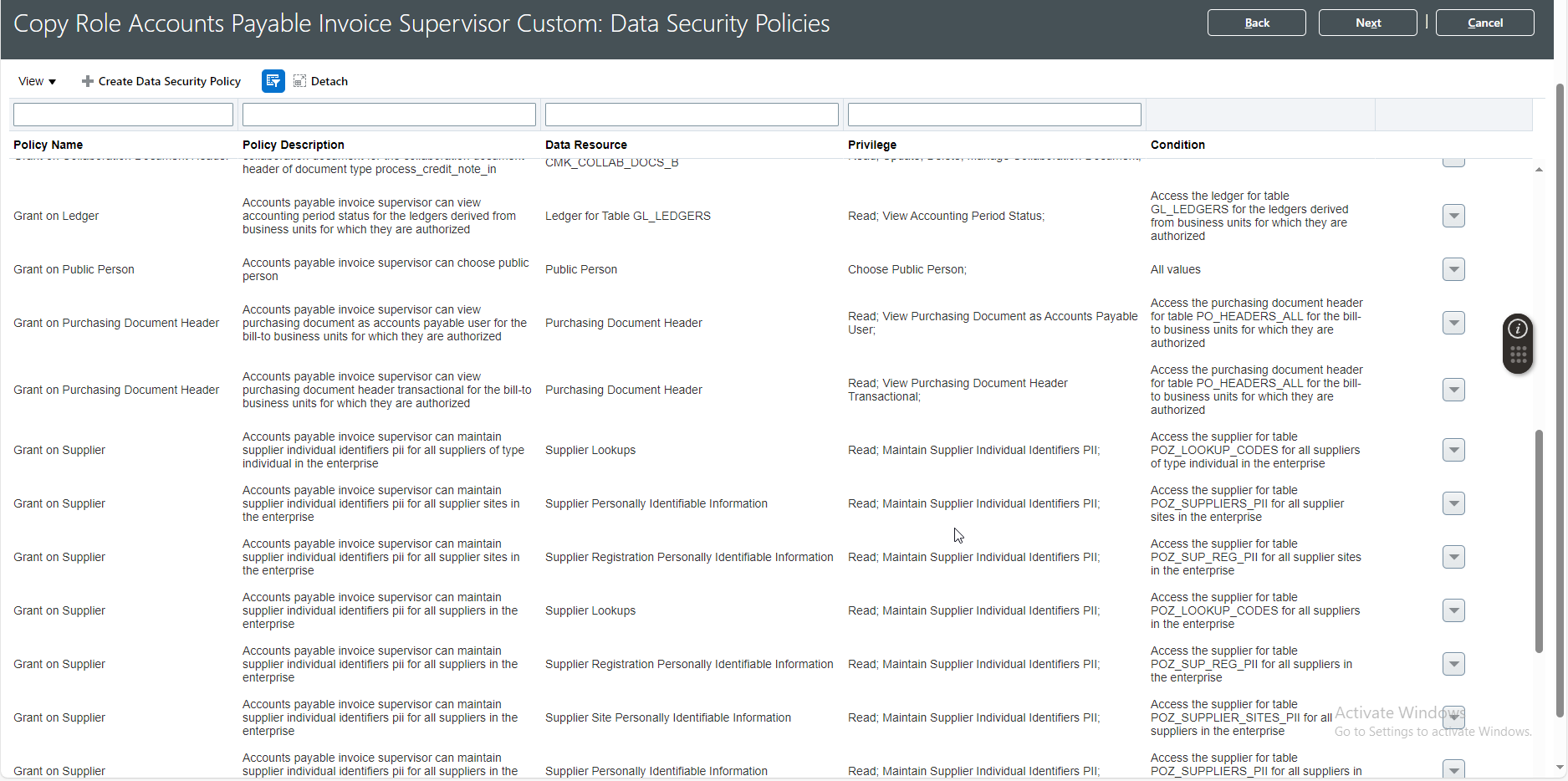
(G.2) Data Security Policies:
This represents “WHO CAN DO WHAT and ON WHICH SET OF DATA”.
This represents a unique association between a duty role and data privilege and condition. A condition is filter or SQL where clause that defines the data set.
Data Security consists of privileges conditionally granted to a role and used to control access to the data.
To enable a user to manage the year-end close task, you must set up the required data security policy for the user’s role. In addition, you must identify the data access set for your ledger and assign them to the user’s role.
Let us consider below screenshot for Data Security Policies: